[ad_1]
Verkada Hack Leaves Lots of of Hundreds of Cameras Uncovered – Right here’s How the Assault Might Have Been Averted With PKI + Entry Management Finest Practices
Ever get the sensation that somebody is watching you? It’s not a pleasant factor, and also you’re much more more likely to expertise it if there are safety cameras in your neighborhood. They’re changing into increasingly frequent today, each in our workplaces and houses, and roughly 5 billion cameras are anticipated to be in use by 2027 based on Reportlinker.com. That’s practically one digital camera for each particular person on earth.
Fashionable video digital camera programs have exploded in reputation due to their low-cost worth and ease of use, however with this comfort issue comes potential safety dangers that may depart us unsuspectingly uncovered. Enter Verkada, a Silicon Valley firm that provides cloud-based safety cameras. Just like the recent SolarWinds hack, every part was wonderful till hackers have been capable of breach Verkada’s programs. Lots of of hundreds of cameras have been compromised, as was the corporate’s video storage library. Abruptly manufacturing facility staff, medical personnel, and even kids taking part in at house have been all uncovered, violating their privateness and doubtlessly permitting attackers to entry different programs on the digital camera’s community.
So, how have been the hackers capable of pull off the Verkada breach? How did the corporate reply? And the way can organizations stop related breaches sooner or later?
Let’s hash it out.
Who’s Verkada?
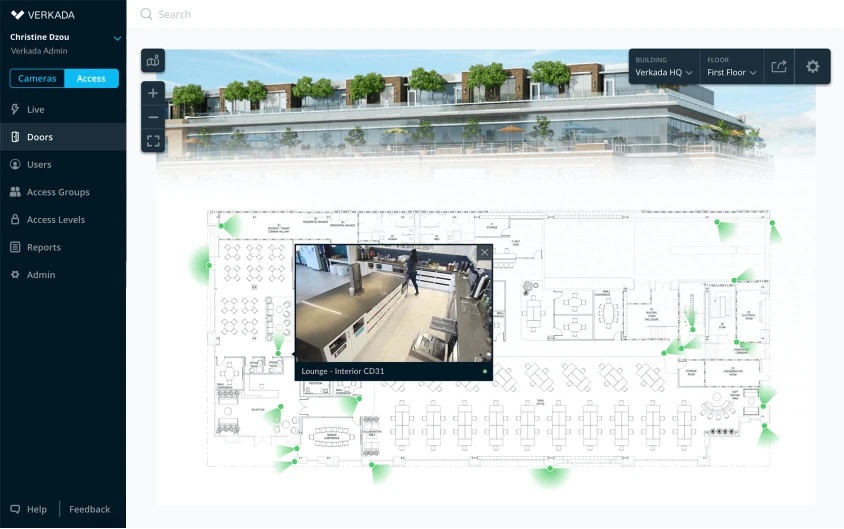
First, let’s check out the corporate itself. Verkada was based in 2016 and sells cameras to all kinds of industries and markets. All the things from workplaces to jails to colleges to gyms to police stations. Notable purchasers of theirs embrace Cloudflare, Tesla, Equinox, and Nissan. Verkada gives the gear required to observe any desired areas, plus constructing automation gear that retains monitor of temperature, movement, noise, and door entry.
Their {hardware} requires an web connection so it may entry their cloud service. This provides clients the flexibility to look at and retailer real-time video from any location. Verkada additionally boasts synthetic intelligence options that may monitor people as they transfer round. Referred to as “Individuals Analytics,” this software program searches for particular folks based mostly on their face, garments, any equipment they’re carrying, and their gender, and permits them to be tracked as they transfer round.
The promoting level of their AI options is that it improves public security and safety by detecting uncommon occurrences that probably pose a hazard. Mainly, the purpose is to cease crimes earlier than they happen. Sure, we’re stepping into Minority Report territory right here. These form of “video analytics” programs have gotten increasingly standard as a higher variety of firms and public organizations flip to them in an try to forestall every part from petty theft to mass shootings.
What Occurred within the Verkada Breach?
About 150,000 of the corporate’s cameras have been accessed by a Swiss “hactivist” group generally known as Persistent Menace 69420 (fairly the intense title, certainly). The collective has lower than ten members, together with Tillie Kottman, who describes their mission:
We usually don’t do focused work. All of us have ADHD and never loads of endurance. We do scans for very broad vectors in search of vulnerabilities.
The purpose of this explicit assault was comparatively easy – to display how simply Verkada’s cameras might be hacked and to boost consciousness of their vulnerabilities. Entry was gained when the group situated credentials for a “tremendous admin” account on a public-facing server. Particularly, it was on an unencrypted subdomain supposed for use as an inner improvement system. As Kottman explains:
This one was simple. We merely used their net app the best way any person would, besides we had the flexibility to change to any person account we desired. We didn’t entry any server. We merely logged into their net UI with a extremely privileged person account.
After discovering the credentials, they have been capable of transfer freely inside Verkada’s inner community and had root entry to particular person cameras. This allowed them to make use of the cameras to execute no matter code they wished, giving them the flexibility to doubtlessly carry out additional, escalated assaults. The hackers have been additionally capable of subsequently infiltrate some buyer networks by utilizing the digital camera’s connection as a place to begin.
In addition to accessing the dwell feeds of particular person cameras, the hacker group was additionally capable of infiltrate the whole video archive that accommodates information saved by Verkada’s customers to the cloud. The centralized nature of the corporate’s software program enabled the attackers to browse a large quantity of knowledge with just some clicks.
Who Have been the Victims of the Verkada Breach?
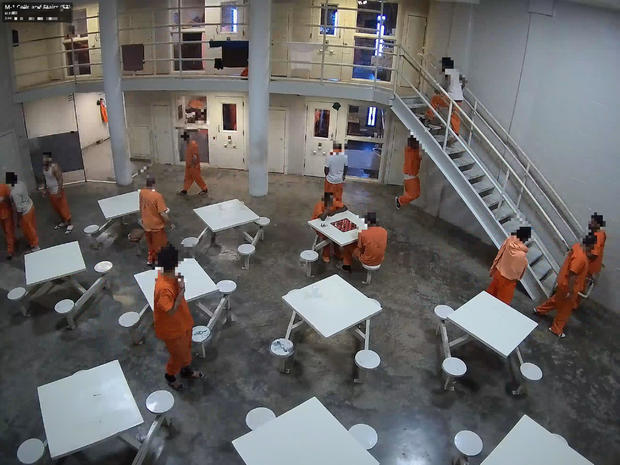
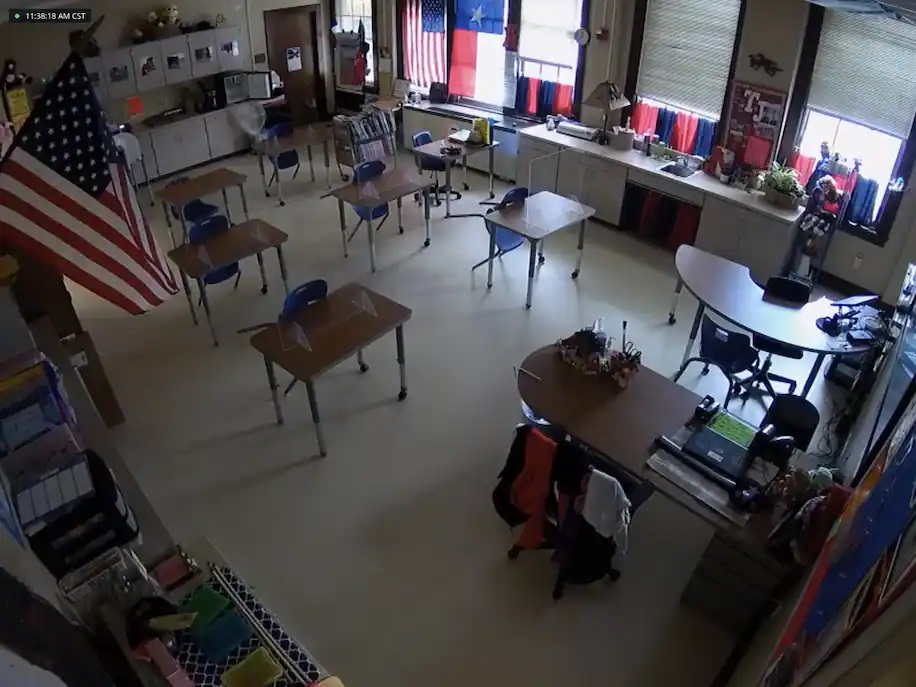
Anybody who used Verkada cameras was in danger, and the listing of these affected is each lengthy and various. The attackers have been capable of take a dwell glimpse into the factories of Tesla and Nissan, county jails across the nation, and the workplaces of firms like Cloudflare and Equinox. Organizations weren’t the one goal – common folks such as you and I have been impacted as properly. The hackers didn’t discriminate.
A few of the launched movies are fairly eerie to look at due to how “actual” they’re and the truth that the topics of the movies do not know they’re being spied on. One video reveals a father and his kids working a puzzle in a playroom, and one other reveals a nurse checking on somebody in a hospital mattress. There’s movies of empty corridors and convention rooms, and even ones of convicts milling round a jail.

The hackers didn’t cease there as soon as that they had entry to Verkada’s community. They stole the corporate’s whole consumer listing, containing over 24,000 entries together with doubtlessly delicate data on every.
How Did Verkada Reply?
The corporate acknowledged the hack and issued an apology for the publicity of “video and picture knowledge from a restricted variety of cameras.” Nonetheless, they aren’t eliminating the flexibility to view the dwell stream of particular person gadgets.
Transferring ahead, Verkada says they intend to provide you with a simpler strategy to managing login knowledge, rent extra safety specialists, and use third-party consultants to carry out a safety audit. CEO Filip Kaliszan stated:
Whereas we have already got strong logging and audit capabilities, we’ll be certain that clients obtain proactive notifications at any time when their knowledge is accessed by Verkada, together with by our technical workers
The corporate has additionally disabled their inner administrator accounts and notified legislation enforcement to allow them to pursue the perpetrators.

Verkada has been within the information a couple of instances beforehand prior to now few years, and never for good causes. Their safety measures have been publicly questioned by safety analysts, with Charles Rollet, a part of the safety analysis group IPVM, saying
Verkada had bought their system as notably superior by way of privateness and safety, which is ironic once you have a look at what occurred. Individuals don’t understand what occurs on the back-end, they usually assume that there are at all times these super-formal processes in the case of accessing footage, and that the corporate will at all times want to provide specific consent. However clearly that’s not at all times the case.
Three workers have been additionally terminated final yr for utilizing firm cameras to spy on fellow workers, in addition to making sexually specific jokes about them. They aren’t the one safety firm to face this sort of situation, because the doorbell firm Ring has additionally not too long ago fired workers for related infractions.
Verkada might face much more authorized bother down the road, because the Division of Well being and Human Companies (HHS) might examine them for attainable HIPAA/HITECH violations. Safety digital camera footage from medical amenities can generally be thought-about as delicate well being data. There are additionally attainable GDPR violations and the potential for class-action lawsuits, so time will inform what extra penalties Verkada could also be hit with.
How Might the Verkada Breach Have Been Prevented?
The Verkada breach raises quite a few questions regarding machine safety. First off, why did this “tremendous admin” account exist within the first place? Verkada stated that admin entry was given to engineers and help workers in order that technical points might be mounted, however certainly there are higher approaches that may nonetheless enable for efficient drawback fixing and troubleshooting. Admin entry ought to solely be given out on a user-by-user foundation, and solely to those who completely require it to hold out their duties. Jeff Costlow, CISO at cloud safety agency ExtraHop, agrees:
I’m OK with distributors being able to auto-update the machine. Which means they’ve management over the supply code. However that doesn’t imply that they’ve management over the machine any time they need.
Corporations, and particularly start-ups like Verkada, should implement greatest practices for privileged entry to programs to be able to stop privateness breaches like these. Whereas manufactures do certainly have authentic causes to log into your gadgets, complete controls, restrictions, and auditing must be enacted to take care of the correct steadiness between security and entry.
There was clearly a scarcity of efficient entry management in place, and even when these form of “tremendous” accounts exist, the credentials ought to by no means be saved anyplace that would doubtlessly be public-facing. This can be a textbook instance of how certificate-based authentication can stop unauthorized entry. Copying and pasting a username and password into an e mail or webpage is a better and extra probably situation than somebody taking an archive of the certificates/key and posting the contents. Plus, you possibly can hyperlink certificates to particular person customers so that you’ll have a path of who’s accessing what, and once they’re doing it.
Distributors might even go a step additional and have every buyer act as its personal “mini” non-public certificates authority. That means, nobody can entry the machine except the proprietor points a certificates to them. Within the case of Verkada, if a buyer had a technical situation then they might situation a certificates to the help workforce so they might repair it. In any other case, the doorways to the machine would at all times be locked.
Finish-users also needs to have extra management over how distributors are capable of work together with their gadgets. Whereas customers can create admin accounts on their very own Verkada cameras, for instance, they couldn’t do something to forestall the corporate’s “tremendous admin” account from accessing their video feed. Ideally, customers must opt-in to permitting a characteristic like that, to be able to protect privateness by default. Customers ought to have full management of the gadgets they personal – interval.
This incident additionally serves as a reminder that upon buying any new machine, one ought to at all times undergo the default settings. You by no means know what’s enabled/disabled by default, and what attainable vulnerabilities could also be created consequently. It doesn’t matter what, the default login credentials ought to at all times be modified.
There’s some irony within the Verkada breach – it demonstrates the risks of self-surveillance. We’ve got such a robust need for a way of safety, but when it’s not correctly applied then it may find yourself creating much more safety threats consequently. On this explicit case, we aren’t even speaking a couple of refined assault or previously unknown vulnerabilities – the unhealthy guys merely used legitimate credentials. It’s crucial that firms be proactive with entry controls and safety basically in order that they received’t must study issues the laborious means, which finally ends up punishing common customers such as you and I, as properly.
Shield Your Web site With CodeGuard Backup

It’s like an undo button to reverse harm carried out by a mistake, cyber assault, a nasty replace, or different points.
[ad_2]
Source link